A comparison of five VPN options and their network and security implications Introduction Virtual Private Network (VPN) is a technology that creates a secure and encrypted connection over a public network, such as the Internet,
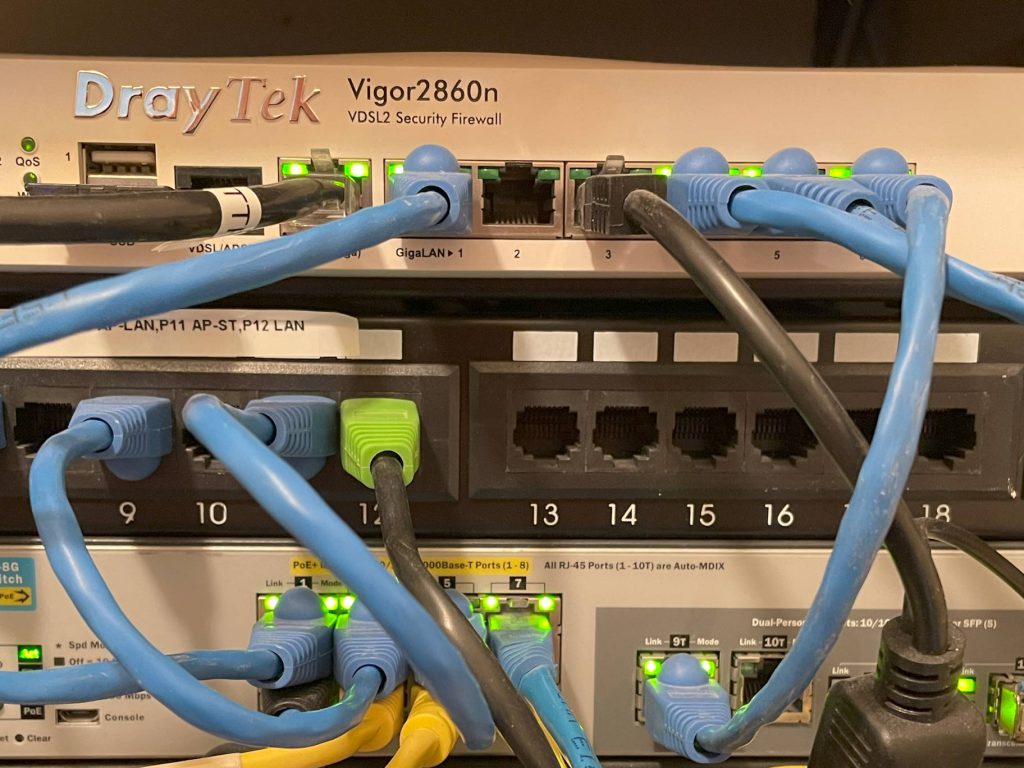
Continue ReadingEntra Remote Network to Draytek 2860n Failure
This article details the configuration issues with a Draytek 2860n VPN into Microsoft Entra. Issue You try to connect your Draytek 2860n but receive the below error in the logs: 2023-10-17 18:36:26 [IPSEC][L2L][1:EntraVPN][@xxx.xxx.xxx.13] IKE link
Continue ReadingHow to create a remote network into Entra Global Security Access
The following steps detail how to create a direct VPN connection using FortiGate Firewall into the Entra Global Security Access service to protect network traffic of all device within your corporate networks. The scenario is
Continue Reading